Partners
Orca Security
Allways active.
Allways safe.
Any cloud.
With Orca Security
Understand and prioritize the greatest risk in the cloud
The Orca cloud security platform easily connects to your cloud environment to provide full coverage of all cloud risks, including misconfigurations, vulnerabilities, identity risks, data security, API exposure, and advanced threats:
- Stop reviewing long lists of alerts and prioritize the main combination of risks that matter
- Automatically identify personal information and valuable assets to avoid critical risks to your business
- Quickly understand contextual risk in multi cloud environments

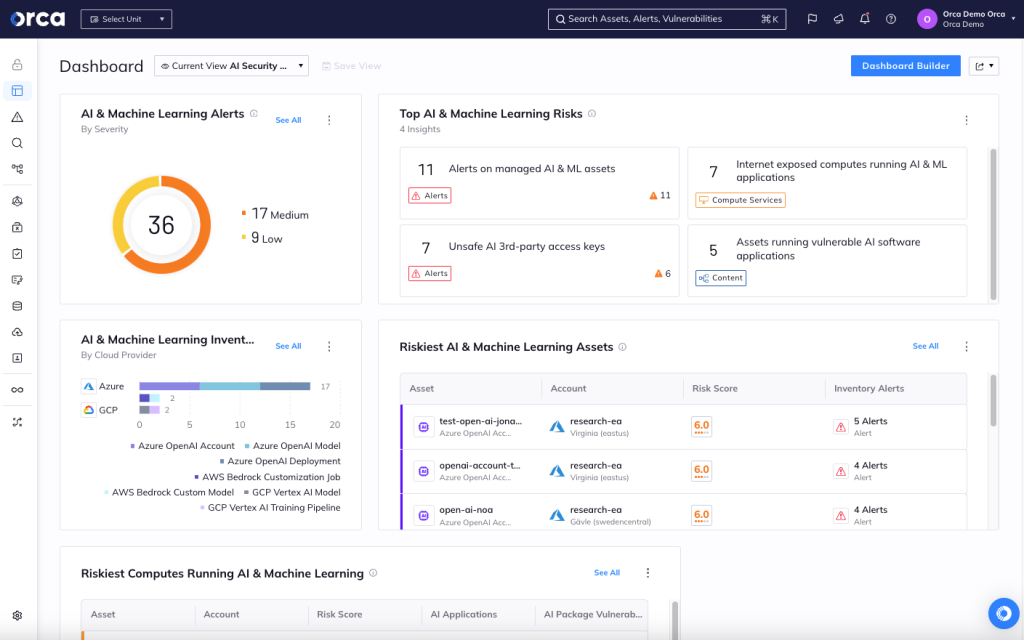
Protect al AI models your organization use
The Orca cloud security platform easily connects to your cloud environment to provide complete coverage of all cloud risks, including misconfigurations, vulnerabilities, identity risks, data security, API exposure, and advanced threats:
Cloud security management
Continuously monitor, identify, and remediate misconfigurations in clouds, including cloud infrastructure posture management, automated remediation, pre-deployment IaC scanning, and reporting.
Cloud infrastructure management
Detects identity misconfigurations, ensures compliance and least-privilege access, and monitors identity hygiene metrics. Integrated with leading SSO and IDP tools.
Patch and vulnerabilities management
Manage vulnerabilities and prioritize risks. Understand operating system vulnerability issues, packages, and other problems in Linux and Windows virtual machines, container images, and serverless functions.
Security changes
Scan Infrastructure as Code (IaC) templates and container images from a single platform, ensuring that any vulnerability, secret, misconfiguration, and malware are detected early in the development process.

